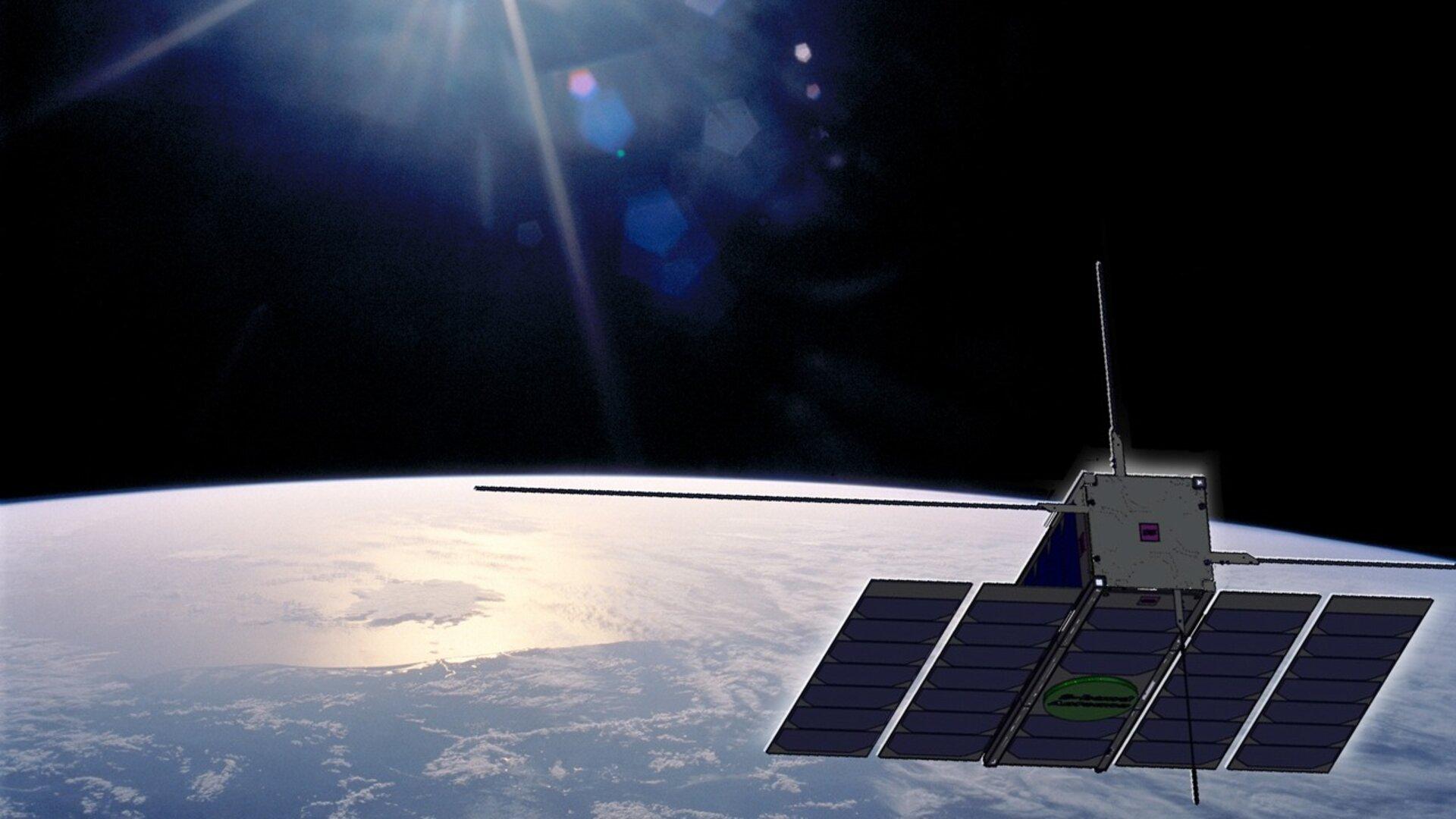
The European Space Agency (ESA) granted cybersecurity company Thales access to the OPS-SAT nanosatellite. This is the first time that a simulated break-in to an ESA device has been performed.
Even the world’s largest space agencies have security breaches in their systems. In this case, the European Space Agency wanted to check the state of cybersecurity in its space technology and allowed the Thales company’s cybersecurity team access to ‘hack’ into the OPS-SAT satellite operating system during the CYSAT conference.
Thales workers were able to access the satellite’s global positioning system, which allowed them to control the satellite’s orientation, position and onboard camera.
“Unauthorized access to these systems can cause serious damage to the satellite or result in a loss of control over its mission.”
The European Space Agency has confirmed that the OPS-SAT satellite was under control at all times and that the Thales company did not perform any risky maneuvers during its return to Earth. They used standard access rights to manage the satellite application environment, and, to their surprise, they found vulnerabilities in the systems that allowed the introduction of malware!
What did Thales do? Using malicious code, Thales was able to compromise the data sent to Earth so that they could modify the images recorded by the orbiter’s camera. Not only that, they were able to hide their activity from ESA by masking selected geographic areas in the satellite photographs.
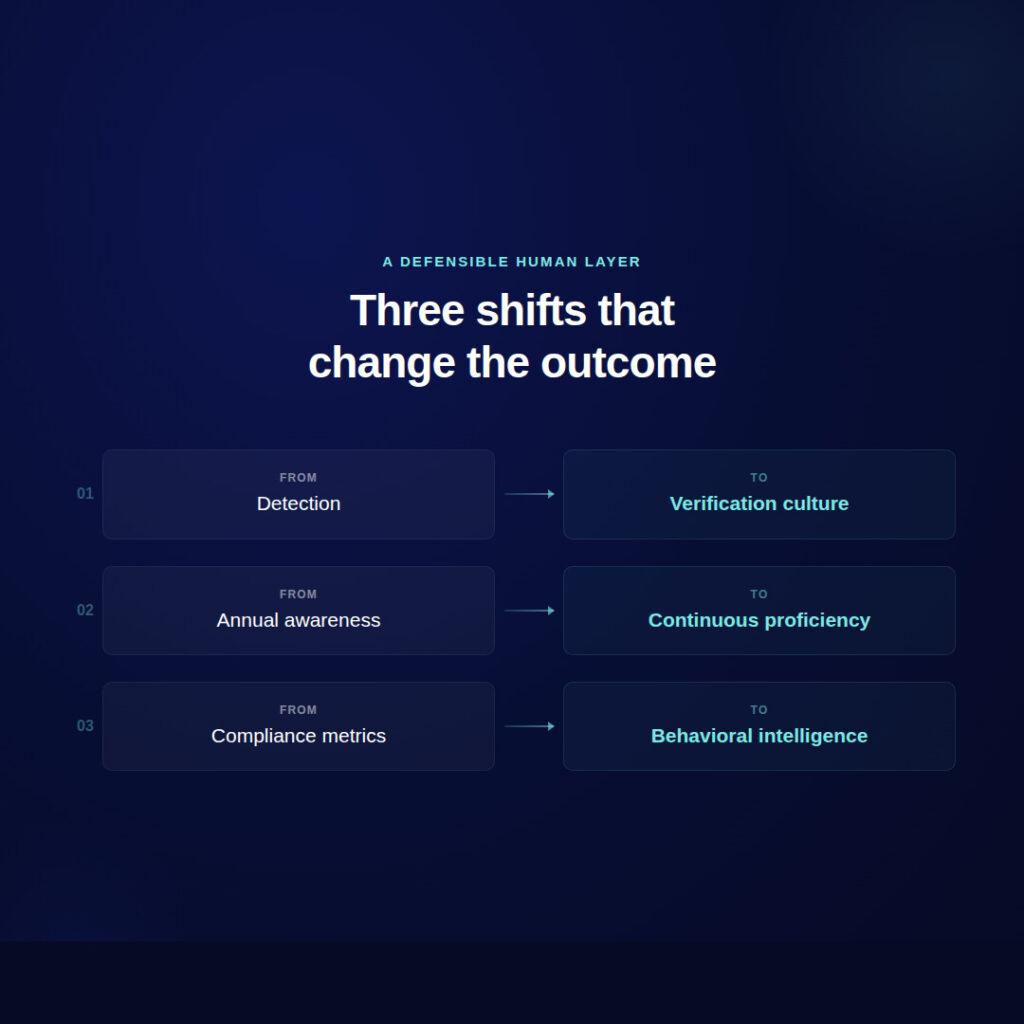
“With the growing number of military and civilian applications relying on satellite systems today, the space industry must consider cybersecurity at all stages of the satellite lifecycle.” said Pierre-Yves Jolivet, vice president of cyber solutions at Thales. The executive also pointed out that the initial design, development, and maintenance of the systems is critical to ensure that the systems can adapt to current and future solutions.