Cristina Dolan was born in New York (1977). She is an engineer and computer scientist with a master’s degree from the MIT Media Lab. He also holds the position of Global Head of Alliances at RSA NetWitness. Throughout his career, he has held executive roles at companies such as IBM, Oracle, Disney and Hearst.
Dolan is also the author of a book entitled“Transparency in ESG and the circular economy, capturing opportunities through data“. Despite her origins in New York, she maintains a strong connection to Spain due to her maternal roots. In fact, he co-founded Additum.es, a company that applies technology in the healthcare sector in our country.
In this interview, Cristina focuses on the threats posed by technology, specifically cyber risks and how they can cause serious damage to companies and humanity, which would be more catastrophic than any natural disaster.
In the interview given by Dolan to the digital media Digital Enterprise Show and picked up by the Manufacturers and Distributors Association, the cybersecurity expert highlighted the cyber risks faced by business organizations that, in Dolan’s words, ‘are the most immediate challenges facing business and humanity’.
“The impact of cyberattacks is far greater than that of any other warfare tactic.”
Cristina, asked by interviewer Charo Toribio about why she considers cyber risks to be more harmful to humanity than even climate change or nuclear war, argues that “…cyber risks are more harmful than climate change or nuclear war.if in a war one country drops a bomb, the other country will respond with another bomb. But when it comes to cyberattacks, which can be even more damaging than bombs, it is more complicated to retaliate with the same scope and intensity.“
An example that illustrates the magnitude of this risk is the statement by Rohit Ghai, CEO of RSA, a company that develops cryptographic systems in collaboration with MIT mathematicians.
Ghai noted that in the Ukrainian war, the number of cyber soldiers outnumber conventional military personnel. This highlights both the power and the risk that cyberspace represents in an increasingly interconnected world.
While climate change and sustainability are major challenges that need to be addressed, in the current era, cybersecurity has become a key risk.
Dolan states that we are living a fourth industrial revolution, characterized by interconnectedness and the application of technology in all areas of our lives.
“In all industrial revolutions there is a positive and a negative side.”
Throughout each industrial revolution, from the first to the present, individuals, communities and companies have become increasingly dependent on each other.
Therefore, sustainability can no longer be analyzed solely from a climatic or social perspective. It should be viewed as a holistic set of risk metrics, in which cybersecurity plays a key role.
Thus, technology is seen as a driving force in this fourth industrial revolution and affects the three main forces described by Professor Jeremy Rifkin in the third industrial revolution: energy (with renewable and distributed sources), communication of economic value (through blockchain) and mobility (with electric, autonomous and shared transport).
However, as has been the case in all industrial revolutions, this fourth one also has positive and negative aspects.
While technology is essential for innovation and problem solving, it comes with cybersecurity risks, so as companies innovate and apply more technology, these cyber risks increase.
To fully understand the scope of these cyber risks, real-life examples are necessary: they can have a devastating impact on a nation’s critical infrastructure.
They can disable power plants, interrupt a city’s water supply and even endanger the lives of its inhabitants. It is important to understand that the impact of cyber attacks far exceeds that of any other warfare tactic.
“The main interest behind a cyberattack is economic, followed by political.”
Dolan has detailed that cyber attacks are driven by a variety of interests. In the first place, economic interest plays a fundamental role.
This is because cyber-attacks can be profitable both through direct theft and through investment in cybersecurity .
An illustrative example is the case of North Korea, where it is estimated that around 8% of the Gross Domestic Product (GDP) is generated by some form of hacking, according to the FBI.
The second interest behind a cyberattack, according to Cristina, is political interest .
These attacks offer the possibility of maintaining an asymmetry in the response. While in a conventional war, a country can drop a bomb and receive a similar response, in the case of cyberattacks, the situation is complicated.
Therefore, cyber-attacks can be both politically and economically motivated. This has been clearly evidenced in the cryptocurrency arena, where thefts in the millions have been occurring on an ongoing basis.
Warren Buffet, for example, has stated that cybercrime represents the greatest threat to humanity, surpassing even the natural disasters that have occurred in the last decade.
Cyber-attacks, in fact, have become the most imminent financial risk today, as Cristina mentioned in a article for the World Economic Forumwhich coincided with Putin’s first cyber-attacks on Ukraine.
“Unfortunately, there are many Boards of Directors who don’t take cybersecurity as seriously as they should.”
On what strategies company executives should pursue to protect their digital assets, Dolan is blunt: Executives need to take a more serious and proactive approach to their companies’ cybersecurity.
In many cases, boards of directors do not consider cybersecurity a priority and mistakenly assume that it is the sole responsibility of the organization’s CIO. This mentality is dangerous, as insurance cannot cover all cyber risks.
It is crucial that cybersecurity is integrated into the governance of the organization and the associated risks are fully understood in order to take appropriate action.
Cristina therefore considers it essential to recognize that a cybersecurity incident can have a devastating impact on a company and can lead to its ruin faster than one might imagine, surpassing even the consequences of climate change.
An illustrative example is the case of Marriott, which faced a massive data breach. Had this occurred after the implementation of California’s data protection law, the resulting fines would have been enough to bankrupt the company.
These cyber and financial risks are very real and can have a ripple effect affecting shareholders, employees, partners, tax collection and ultimately the entire community.
“Corporate CEOs are beginning to understand the importance of properly assessing and managing cyber risks.”
Dolan brings some optimism for the industry, and emphasizes that company CEOs must develop effective detection and response plans to address cyber risks immediately, something that is slowly catching on among senior management.
In addition, collaboration between companies is essential, as many of the cyber risks come from other organizations. How is this possible? Because any entity connected to a network must take care of its cybersecurity, otherwise it could become a threat to the entire ecosystem, spreading like a virus.
Thus, the impact of a lack of sustainability in organizations can be devastating to communities, and this is evident when looking at cases such as the city of Rochester, New York, which was once thriving thanks to companies such as Kodak and now faces decline .
The relationship between companies, communities and the technology ecosystem is fundamental and must be understood in its entirety.
The Internet of Things and the cyber risks of its accelerated evolution
The boundless expansion of the Internet of Things (IoT) is an undeniable phenomenon. Today, IoT devices account for 54% of the 21.7 billion connected devices, and are projected to exceed 30 billion by 2025, which equates to approximately four devices for every person.
This growth covers various fields of application, from wearables that monitor physical activity to sectors such as agriculture, automotive, health, industry, education and home automation.
According to Gartner (IT research and consulting firm), 45% of organizations are expected to suffer a supply chain attack in the next two years.
And, to top it off, 60% of SMEs experienced some type of cyber-attack in the last year according to the firm.
Small businesses, which play an important role in job creation in many economies, have seen an alarming 424% increase in cyber breaches in the past year.
This reflects that the potential for damage is immense. Statistics from the National Cyber Security Alliance don’t lie: 60% of companies that suffer a data breach go out of business within six months.
To be more precise: expect the global cost of cybercrime to reach $10.5 trillion by 2025.
The weakest link: the human being
Cristina Dolan warns that the increasing use of artificial intelligence with generative and predictive capabilities based on learning password leaks has given rise to tools such as PassGen.
The expert explains that these tools can guess 51% of passwords in one minute, 65% in one hour, 71% in one day and 81% in one month. Therefore, it is crucial to take measures to protect credentials and passwords.
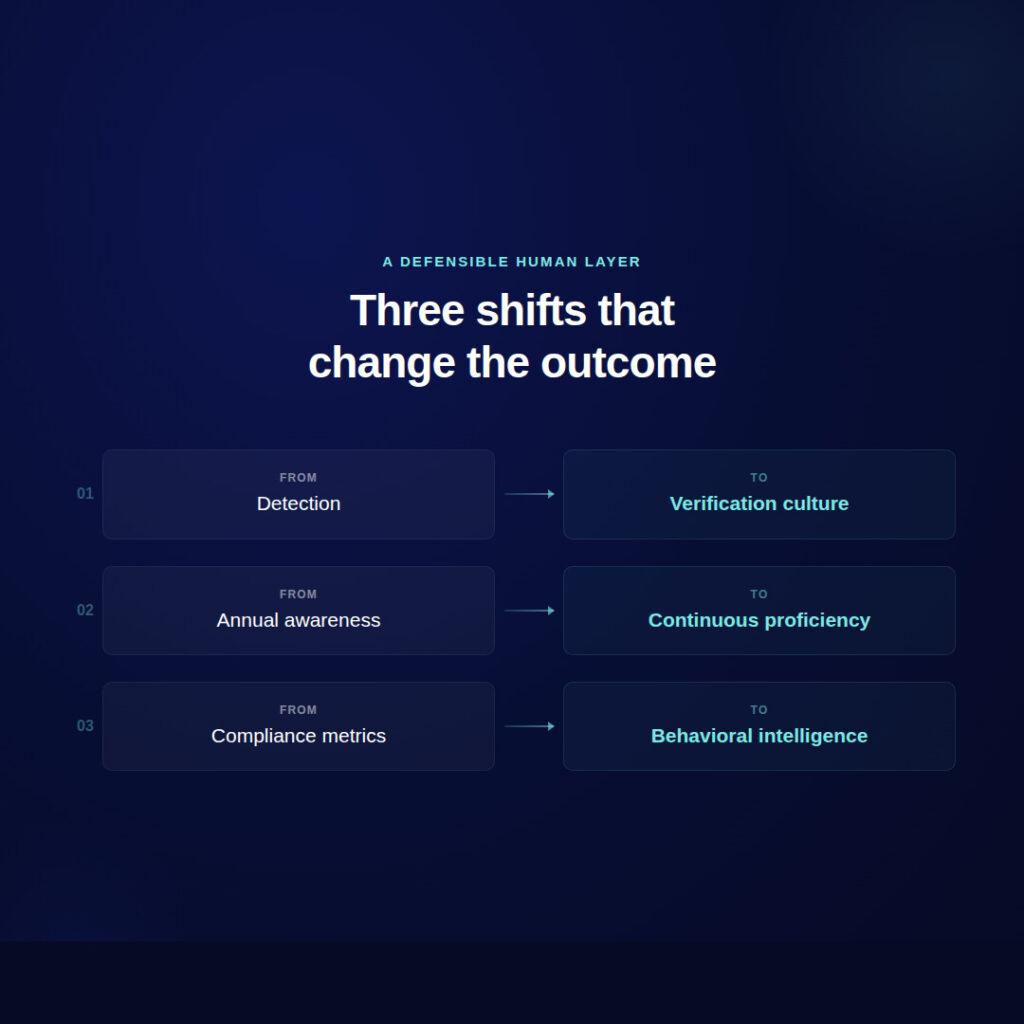
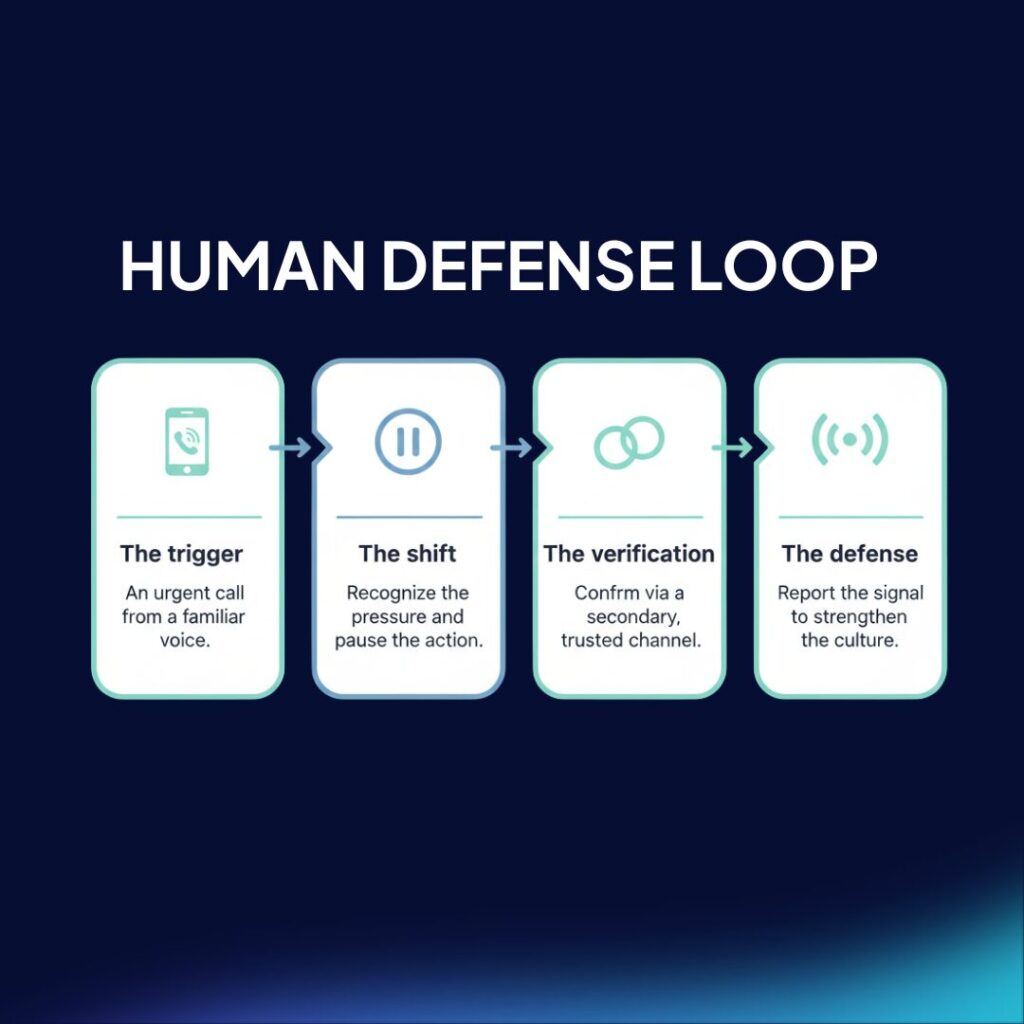
In addition, citizen education and awareness of cybersecurity is essential, especially for the most vulnerable segments of the population. This can only be achieved by building an effective human firewall, so that company employees are aware of the cyber risks to which they are exposed.
Thus, the importance of developing a human firewall lies in the need for companies to protect their assets (mostly digital), as well as to avoid reputational losses if a cyber-attack were to occur and customer data were compromised.
As a result, mobile devices account for a significant portion of digital fraud, and most users lack the knowledge to protect their data.
In summary, cybersecurity has become a critical cyber risk today due to the increasing interdependence between technology and business in this fourth industrial revolution.
While sustainability and climate change are important, other key factors cannot be underestimated. Companies must address cybersecurity as an integral part of their strategy to ensure their survival and protect themselves in this new digital environment.
Zepo, your best ally against cyber risks
Register your employees.
You can do this manually or with a CSV file.

Launch controlled phishing attacks and put your teams to the test.
You will be able to check in real time who has fallen into the trap.

Train them in cyber-attack prevention.
Create customized prevention courses